Security Testing is a type of software testing that uncovers vulnerabilities in the system. It also determines that the data and resources of the system are protected from possible intruders. It ensures that the software system and application are free from any threats or risks that can cause a loss. Security Testing Services of any system focus on finding all possible loopholes and weaknesses that might result in the organization's loss of information or reputation.
People around the world call security testing with different terms as well. It is also known as Penetration Testing or Fuzzy Testing. In simple terms, it is a web application testing technique to verify the security of an application against unauthorized users or hackers.
Table of Contents
- Why security testing?
- Why should you do security testing manually?
- Security hack techniques and manual prevention
- Conclusion
Why Security Testing?
Security testing is required to identify vulnerabilities and potential threats. It also helps to check that the system is protected against unauthorized access, data breaches, and other security-related issues.
Why Should You Do Security Testing Manually?
The primary purpose of manual security testing is to find security weaknesses and potential vulnerabilities in a web application that might not be understood or revealed completely by automated security testing alone. Regardless of the number of automated testing software and tools one might use, it is crucial to do manual security testing to analyze software behavior and ensure its integrity, confidentiality, and availability principles are not being violated.
Security Hack Techniques And Manual Prevention
Here we have covered some of the security hack techniques where experts must consider a manual testing approach.
URL manipulation
It is used for web security testing. URL Manipulation attack is when someone edits the URL text in the browser to check the website. URLs are easily changed, which makes inviting target attack or lead to unintended behavior from the server.
How to Test:
Log in to the application with valid credentials. Then copy the URL and paste it into another browser. Now check that it must be redirected to the login page and ask for credentials for login.

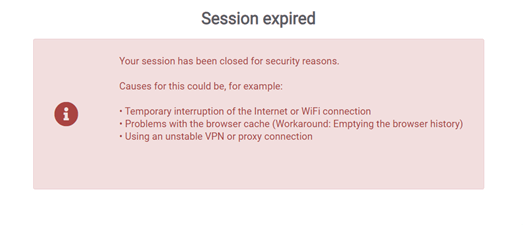
Session expiry
This timeout defines the amount of time a session will remain active in case there is no activity by the user. After the defined idle period gets over, the session is marked as closed or invalidated.
How To test:
Check that the application automatically logs out from the account when the user has been idle for a certain amount of time, ensuring that it is not possible to "reuse" the same session. Also, make sure that no sensitive data remains stored in the browser cache.
Example: In the banking domains, when the session expires and the user clicks OK, it should navigate to the login page.
Privilege Escalation
Hacker gains access to a user's account, bypasses the authorization channel, and successfully grants themselves access to data they are not supposed to have.

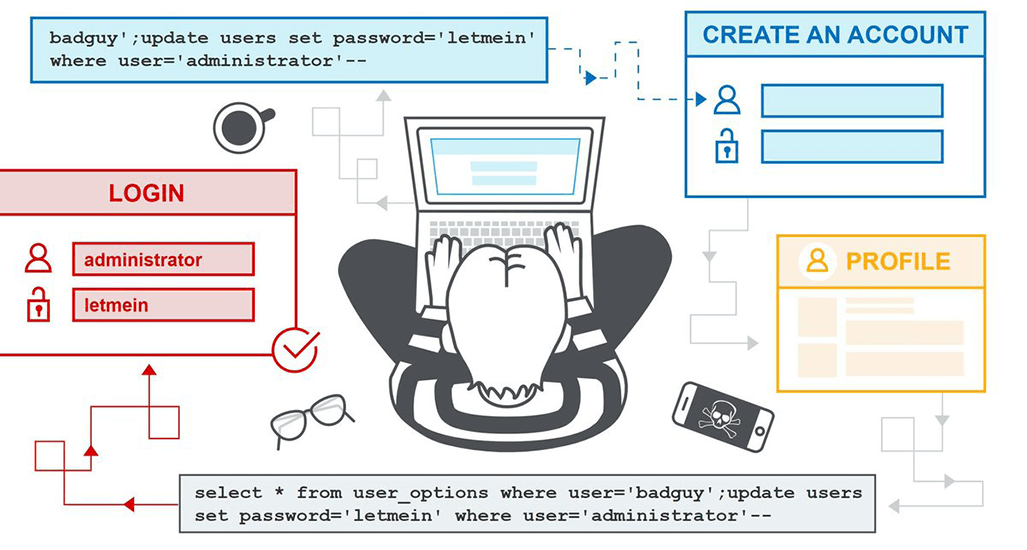
SQL Injection
SQL injection (SQLi) is a web security vulnerability that allows an attacker to interfere with the queries that an application makes to its database. It generally allows an attacker to view data that they are not normally able to retrieve.
How to test:
Hacker injects SQL Commands in on UI, select * from school where 1=1
SQL injection can be prevented by using parameterized queries (also known as prepared statements) instead of string concatenation within the query.
Cookies-based testing
A cookie is a small piece of information stored in a text file on the user's (client) hard drive by the web server. There are two types of cookies we have covered over here:
- Session cookies
Session cookies are active till the browser is open. When we close the browser, this session cookie gets deleted. So, as a tester, you need to check both scenarios.
- Persistence cookies
As per the name, it is stored in a computer's memory and won't delete. It required expiry or user interaction.
_638215524898352652.png)
Cross-site request forgery (CSRF) attack
CSRF is an attack that forces to execute unwanted actions on a malicious web app/website to get the desired result requested by the user, even though the user has already authenticated on the genuine website.
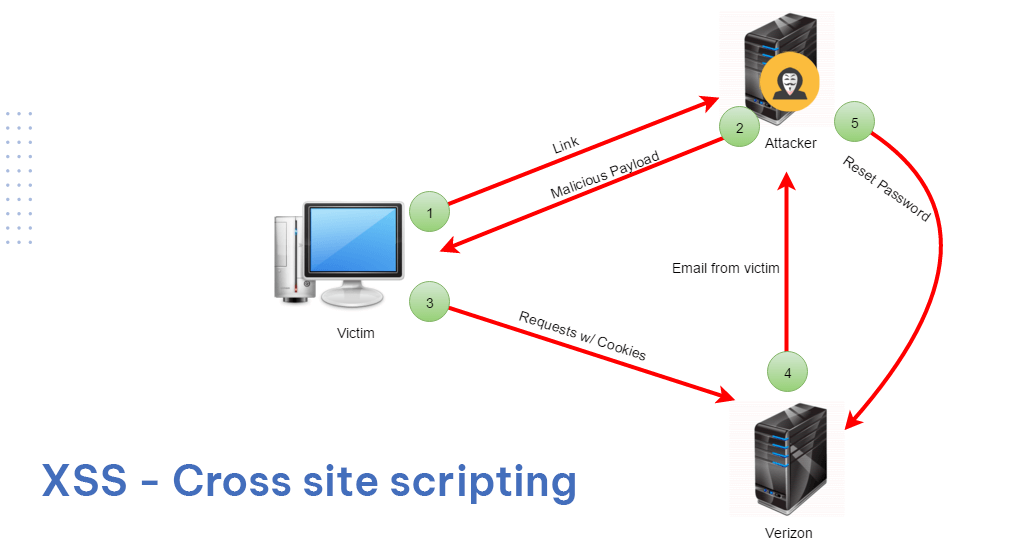
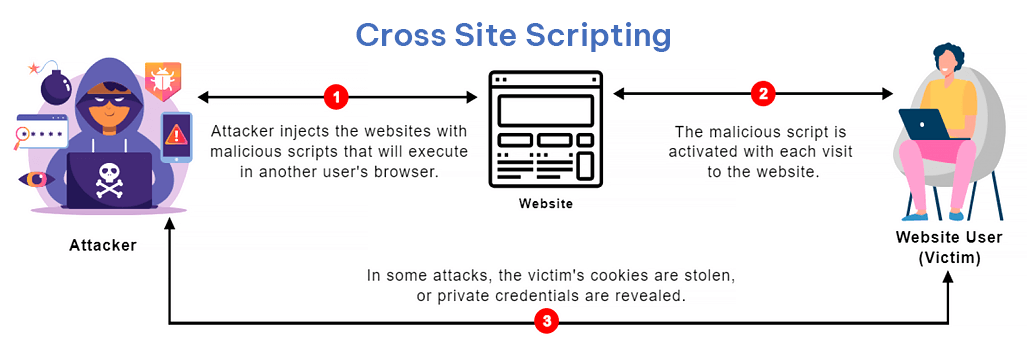
XSS - Cross-site scripting
Something that looks like Froud or a pop-up when you are into banking or sensitive website login leads to a data breach.
Cross-site Scripting (XSS) is a client-side code injection attack. The attacker targets to execute malicious scripts in a web browser of the victim/user by including malicious code in a legitimate web page or web application. The actual attack occurs when the victim visits the web page or web application that executes the malicious code. The web page or web application becomes a vehicle to deliver the malicious script to the user's browser.
Password Management
Password management is a set of principles and best practices to be followed by users while storing and managing passwords efficiently to secure as much as possible to prevent unauthorized access.
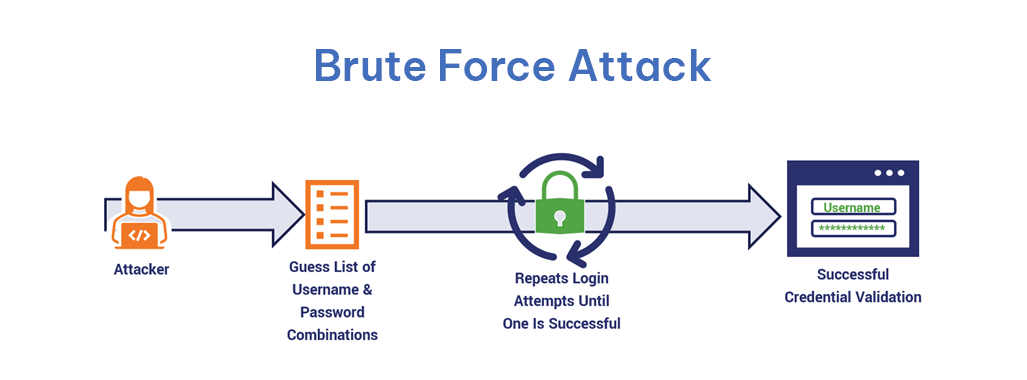
Suppose the web application or system does not enforce stringent password policies, for example, with numeric, special characters, or passphrases. In that case, it may be pretty easy to brute-force passwords and access the account.
Brute Force Attack
Brute-force attacks rely on guessing different combinations of a targeted password until the correct password is discovered.
Conclusion
Security testing can be done automatically, but you must consider manual security testing to secure your web application or website from overlooked vulnerabilities. Experts at PixelQA, a leading Software Testing Company, can help you make your application more secure and bug-free by using the latest techniques and years of experience.
About Author:
 Kevin Patel started his career as QA in Feb 2016. Currently, he is associated with Pixel QA as a Senior QA engineer. He has achieved two major certificates in QA Testing in different domains like accounting, e-commerce, healthcare, and payroll.
Kevin Patel started his career as QA in Feb 2016. Currently, he is associated with Pixel QA as a Senior QA engineer. He has achieved two major certificates in QA Testing in different domains like accounting, e-commerce, healthcare, and payroll.
He loves challenges, team handling, and client communication. He would like to progress in his career as a QA Consultant in the IT field by achieving more QA standards.
